AD links
AD Links is an additional module in Insight. It allows users to log in to Insight using their Active Directory account. This is essential for student logins and optional for staff logins.
As AD Links is an additional module of Insight, a separate charge applies. Please contact sales@tascsoftware.co.uk for further information.
Contents
Configuration
Importing Identifying Numbers into Active Directory
An identifying number must appear in each AD record in order for Insight to link with the Active Directory. It is recommended to use the Admission Number for students, although the UPN or SIMS PersonID can also be used. For staff only the SIMS PersonID can be used.
A list of staff PersonID numbers can be obtained from Insight. Go to:
Accounts > AD Links
Click the Staff report button to download a file containing the PersonID numbers for all staff. The file is in XML format but you can open it in Excel
It is possible to use SIMS AD Provisioning to import Admission Numbers into the Active Directory for students. Alternatively you can use a script from TASC Software to perform this provisioning for you. The TASC script can also be used to import SIMS PersonID numbers for staff. The TASC script will enter the chosen identifying number into the EmployeeID field in Active Directory.
If you wish to use the TASC Software script you will need a CSV file called INPUT.CSV in the format. The file must have exactly two columns; the first column must show the AD Username and the second column must show the identifying number.
The script file can be downloaded here: import.vbs
(right click and select Save As to download)
Once you have downloaded the file, edit it in Notepad (right click and select Edit). The first line of the file will read:
CONST strDomain="MyDomain"
You need to edit this so that your domain appears between the quotation marks, instead of MyDomain. Save the file, then place it in a new folder with your CSV file. The folder must contain nothing else. Double click the import.vbs file to run the script which will update your Active Directory.
Settings within Insight
The following settings are entered into the AD Links page, which is accessed via:
Accounts > AD Links
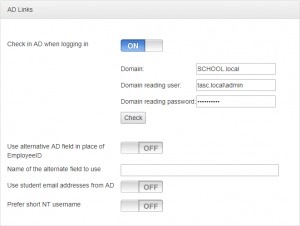
Check in AD when logging in must be enabled for Active Directory logins (if this is switched off, all AD logins will be disabled).
Next enter the Domain, Domain reading user and Domain reading password fields.
The domain should be in the form: mydomain.local. Click the Check button when you have entered these details to confirm that Insight can access the Active Directory.
In some cases you may see a message reading "A trust relationship does not exist between ..."; This should not cause any issues or be a cause for concern.
By default Insight will check the EmployeeID field for the Admission Number (ADNO) to identify students. This will also be required for staff if you want them to log in using the Active Directory details, but they do not have trusted login accounts in SIMS.
Enable the Use alternative AD field in place of EmployeeID option if you would prefer to use an AD field other than EmployeeID. You then need to enter your choice of field into the Name of alternative field to use setting.
Use student email addresses from AD
The alternative is to use the email addresses in SIMS
Single Sign On
An additional benefit of using this method to log in is that it supports Integrated Windows Authentication in supported browsers. This means that if the user is logged onto a computer within the domain, their account information can be used to log into Insight seamlessly (e.g. without entering their account details again).
To implement seamless login, direct those users who you expect to be able to login using their Active Directory details to the ADSSO.aspx page initially. For example:
| Use this address: | https://insight.myschool.co.uk/ADSSO.aspx |
| Rather than this: | https://insight.myschool.co.uk/secure.aspx?ReturnUrl=%2f |
If the user is not already logged into the domain, they will be redirected to the normal login page, where they can still enter their Active Directory username and password. If you do not expect a user to be able to log in this way, they should be directed to the normal login URL.
Troubleshooting
Accounts Not Linked
Check on the Users page:
Accounts > Users
The students' Insight accounts should include @DOMAIN (where DOMAIN is replaced by your AD domain). If any of the students' accounts do not contain this, then those accounts are not linked to the Active Directory and will not be able to log in. You can search for these accounts by filtering to see those where the username does not contain @.
If you find any accounts that are not linked to AD, then log in to Active Directory and check that the student's AD record has the correct identifying number in the correct field. If the AD record appears to be correct then log in to SIMS and check that the identifying number in AD is correct. Once the necessary corrections have been made, perform a Synchronisation via the Users page.
Activity Report
If students' accounts are linked to the Active Directory but they are not able to log in using their AD details then visit the AD Links page via:
Accounts > AD Links
Click the Activity Report button. This will open a window showing the most recent login attempts from AD linked users. This report will tell you if a user has entered an incorrect password. If a user's login attempt does not appear on this report then they are attempting to log in using a username that Insight does not recognise.
Expose AD Fail
There is a setting in the web.config file that can be changed, which will display information about the Active Directory on the login page. To enable this setting edit the web.config file for Insight, which is typically found via:
C:\inetpub\wwwroot\INSIGHT\web.config
Near the bottom of the file is a setting called ExposeADFail. Set the value of this setting to Yes e.g.
<setting name="ExposeADFail" serializeAs="String"> <value>Yes</value> </setting>
Once the value is set to Yes, save the file then attempt to log in to Insight using one of the AD accounts experiencing the problem. The login attempt and you will see a warning message on the login page such as "Invalid username". Hover over the warning message to see further details about the Active Directory connection and login attempt.